HOME / TACTICAL PARTNER PROGRAMME
TACTICAL PARTNER PROGRAMME
Align with a leading cyber security lifestyle brand. Earn recurring commission while NEWORDER handles all technical execution.
TCR PARTNER PROGRAMME
THIS IS NOT A TYPICAL AFFILIATE PROGRAMME

EXTERNAL THREAT EXPOSURE IDENTIFIED WITH TACTICAL PRECISION
- Align With a Leading Cyber Lifestyle Brand — Professional positioning that differentiates you
- Introduce a Service With Real Executive Demand — Solves a problem every board is asking about
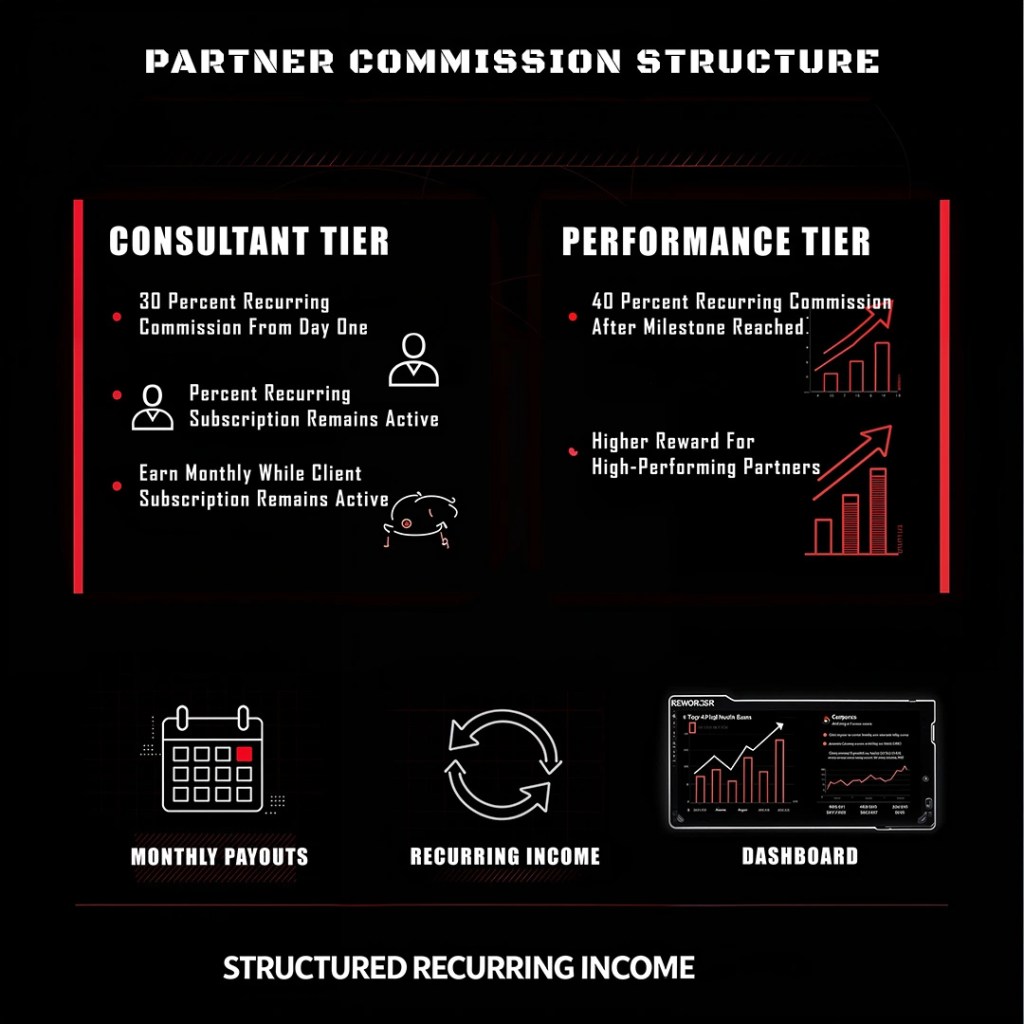
- Earn Recurring Commission — Not one-time payouts. Long-term client relationships
- NEWORDER Handles All Technical Execution — You focus on relationships
- Controlled Partner Intake — Selective programme protecting partner opportunity
- No Cyber Expertise Required — NEWORDER manages everything technical
WHO THIS IS FOR
WHAT YOU INTRODUCE
WHAT NEWORDER HANDLES
HOW IT DIFFERS


CYBER RISK COMPONENTS
20 ASSESSMENT AREAS
All intelligence gathered during the assessment is consolidated into a structured view of your organisation’s external cyber risk posture. This provides leadership with a clear understanding of where exposure exists and which risks require immediate attention.
Adversaries begin with reconnaissance. Domain Intelligence maps the full domain footprint associated with your organisation, including primary domains, subdomains, and supporting infrastructure. This reveals unmanaged or forgotten assets that attackers can leverage as entry points.
Cloud platforms and SaaS environments expand rapidly, often faster than security oversight. This assessment identifies externally visible cloud services, storage instances, and application environments that could unintentionally expose data, access controls, or system interfaces.
Development environments frequently expose information unintentionally. This component searches for publicly accessible code repositories and development artifacts that may contain API keys, credentials, tokens, or internal configuration details.
Documents and operational data shared through collaboration platforms can become publicly accessible without proper controls. This assessment identifies sensitive files or internal information that may be unintentionally exposed through online sharing services.
Cyber adversaries often target organisations based on public signals such as financial activity, operational changes, or public perception. This component monitors open-source intelligence indicators that could reveal when your organisation may be perceived as a valuable or vulnerable target.
Information that once appeared online rarely disappears completely. Archived web intelligence analyses historical versions of websites and internet records to uncover sensitive information, system references, or files that remain accessible through archived internet sources.
Threat actors frequently discuss targets, trade stolen data, and sell compromised credentials in underground forums. This component searches dark web environments for indicators that your data, credentials, or systems may already be circulating among cybercriminal groups.
Attackers analyse the technologies used by their targets to identify known weaknesses. This component maps the externally visible technology stack, identifying outdated platforms, exposed services, and potential vulnerability indicators.
Publicly shared information on social platforms provides attackers with valuable reconnaissance data. This assessment identifies exposed employee information, operational details, or impersonation risks that could be used to conduct targeted social engineering campaigns.
Search engines can unintentionally expose sensitive information when systems are misconfigured. This component identifies publicly indexed data, exposed directories, or internal information that attackers could easily discover using advanced search techniques.
Email remains one of the most effective attack vectors. This assessment evaluates your domain and email infrastructure to identify weaknesses that attackers could exploit to impersonate your organisation or conduct targeted phishing campaigns.
Identifies suspicious domains, impersonation risks, fraudulent digital assets, and abandoned or misconfigured domains that could allow adversaries to impersonate your organisation.
This assessment identifies exposed credentials, vulnerable systems, weak external controls, and technical patterns that ransomware operators commonly exploit to gain initial access to organisations.
Evaluates potential cyber risks introduced through vendor relationships, external platforms, and third-party services that interact with your digital ecosystem.
Identifies signs of exposed or leaked datasets, sensitive files on collaboration platforms, and organisational data that may already be accessible to threat actors or data brokers.
SEE NEWORDER IN ACTION
PROFESSIONAL EXECUTION UNDER PRESSURE
CYBER SECURITY IS THE NEW EXTREME SPORT

Just as extreme sports demand careful planning, the right partnerships, protective gear, and the discipline to push limits, cyber security requires the same relentless preparation, precision, and willingness to operate at the edge.




Similar to extreme sports, Cyber Security requires careful planning and preparation to succeed. It’s pivotal to have the correct partnerships, protective gear, and support in place to ensure that you are fully equipped for any challenge. To be effective in Cyber Security, you must be willing to continuously push yourself to the limit and apply a disciplined approach to every aspect of your daily routine. In Cyber Security, success is not only about reacting to threats as they arise but also to be adequately prepared for them in advance. Extreme sports expose the truth about performance. Preparation matters. Precision matters. Discipline decides the outcome. When professionals execute, it looks effortless. When amateurs try the same move, the consequences are immediate.
CYBER SECURITY WORKS THE SAME WAY
Attackers only need one mistake. One blind spot. One moment of poor execution. Without preparation, the risk becomes real very quickly. At NEWORDER, we use extreme sports to demonstrate what professional execution looks like under pressure. The training, the planning, the discipline, and the willingness to operate at the edge of performance all mirror how modern cyber defence must operate.
WE DO NOT BELIEVE IN PASSIVE SECURITY. We believe in preparation, precision, and controlled risk. Just like extreme sports, cyber security rewards professionals who train for the moment before it happens.
